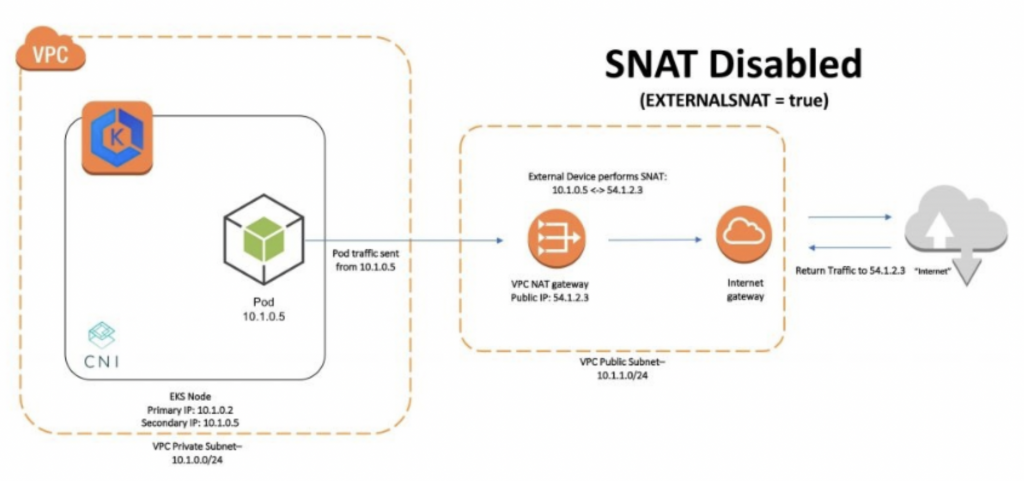
If part of our application is executed in an EKS cluster, either one or several availability zones, it is likely that it will be necessary to access some service through the Internet that is protected by a firewall. In these cases, the dynamic nature of the cluster nodes can complicate access by having to constantly maintain the list of node IPs, as these can change.
To solve this problem, we can create a common Internet gateway for all nodes in each of the availability zones, so that we only have one IP for each zone of the cluster. Resulting in a scheme like the following:
Procedure to follow
1. Create a private and public subnet for each of the three availability zones, in this case, eu-west-1a, eu-west-1b, eu-west-1c.

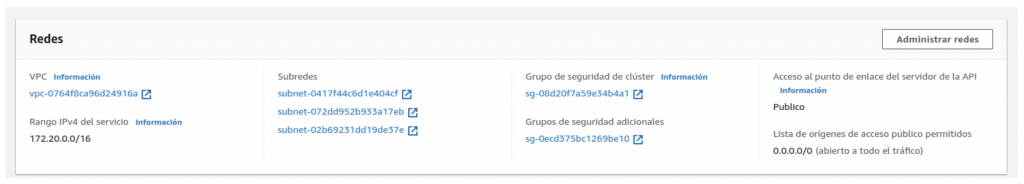
2. Update the EKS cluster, to include the 3 private subnets as subnets of the nodes.
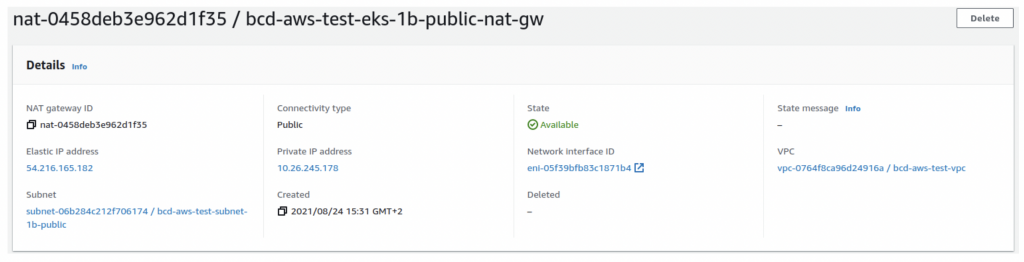
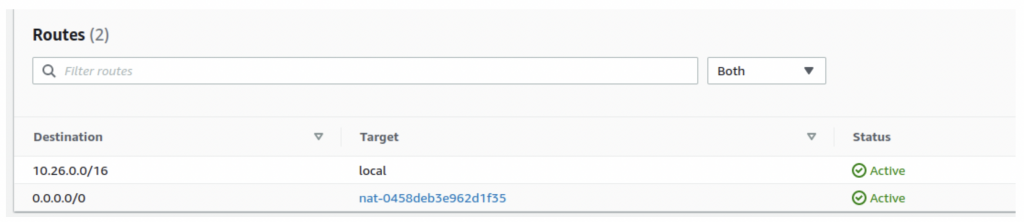
3. Create 3 nat gateways, with their respective elastic IPs, for each public subnet.
4. Create 3 routing tables for the private subnets, routing 0.0.0.0.0/0 to the respective nat gateway of each private subnet.
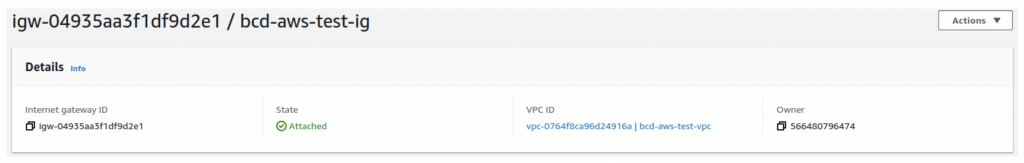
5. Create an internet gateway.
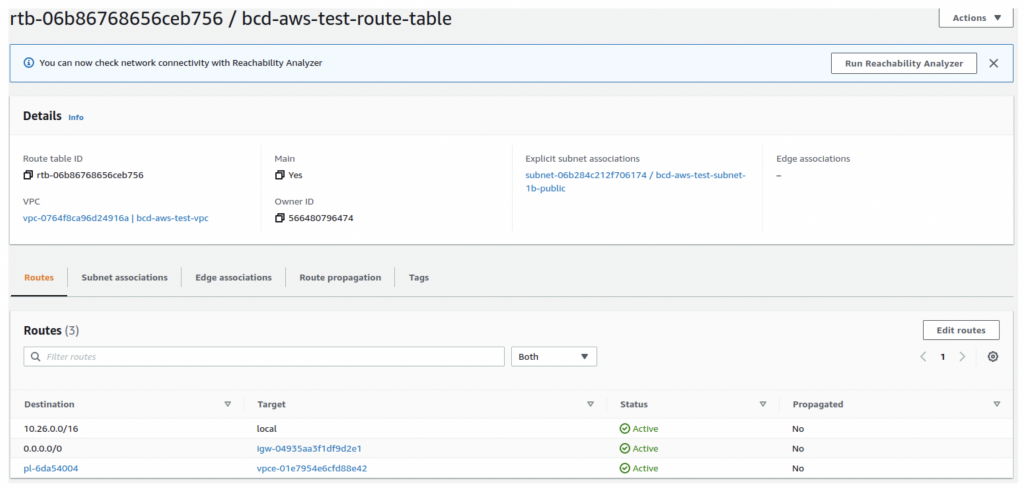
6. Create 3 routing tables for the public subnets that route the desired traffic, in this case 0.0.0.0.0/0, to the created internet gateway.
7. Mark the use of external SNAT as true using kubectl:
kubectl set env daemonset -n kube-system aws-node AWS_VPC_K8S_CNI_EXTERNALSNAT=trueConclusion
It is true that the implementation of this method may be limited by the number of static IPs available on AWS, which by default allows the creation of 5 IPs. In addition, it will be necessary to recreate the services receiving internet traffic to adapt them to the new network.
More information about the proposed solution and SNAT can be found at this link in the amazon documentation.
If you found this article interesting, we encourage you to visit the Software category to see more posts like this one and to share it on social networks with all your contacts. Don’t forget to mention us (@DamavisStudio) to let us know what you think.